Social engineering is a method of obtaining private information, access, or valuables by exploiting other people’s mistakes.
These so-called “human hacking” scams are frequently used in cybercrime to trick unsuspecting users into revealing data, spreading malware infections, or granting access to systems that should be kept private.
To gain unauthorised access, the hacker could use the phone, email, snail mail, or even face-to-face contact. Phishing, spear phishing, and CEO fraud all demonstrate this.
Watch this youtube video to learn how to prevent social engineering attacks:
Penetration Testing. The most effective approach among the ways to prevent social engineering attacks is conducting a pen-test to detect and try to exploit vulnerabilities in your organization.
Now let us discuss the most effective way to detect and stop social engineering attacks?
Most effective ways to detect & stop social engineering attacks
1. Multi-Factor Authentication

Don’t rely on just one thing. Even the simplest precaution will keep your account safe.
The password makes sure security, but we’ve learned that it’s not enough on its own. Because it’s much easier for someone to figure out your password and get into your accounts if they try a lot of different ones.
Social engineering can be used to get to the passwords. Multi-Factor Verification is needed, which could be anything from a security question to a biometric access code to an OTP code.
2. Keep an eye on important systems all the time

Make sure that your system, which has sensitive information, is being watched 24 hours a day, seven days a week.
When exploiting methods like Trojans are used, they sometimes depend on a system that is weak. Web application scanning can help you find holes in your system by checking both external and internal systems.
Also, you should do a social engineering engagement at least once a year to see if your employees are likely to fall for social engineering tricks.
Once found, if there are any fake domains, they can be shut down right away to avoid copyright violations online.
3. Use a cloud-based Next-Gen WAF (Web Application Firewall)

Your business probably already uses a firewall, but a next-generation web application cloud-based firewall is made to protect against social engineering attacks as much as possible.
Most companies use a traditional WAF, which is very different from the web WAF.
To be more specific, AppTrana can constantly watch a website or web application for strange or bad behaviour.
Even though social engineering attacks rely on people making mistakes, it will stop attacks and warn you if someone tries to install malware.
One of the best ways to stop social engineering attacks and any possible infiltration is to use a risk-based WAF.
4. Verify Email Sender’s Identity
Most scams involve pretending to be a trusted organisation in order to get information from the victim.
Especially in a phishing attack, attackers send emails that look like they came from a sender you trust, like a credit card company, bank, social networking site, or online store.
Most of the time, the emails tell a storey to get you to click on the fake link, which looks real.
To avoid these kinds of social engineering threats, contact the person who said he sent the email and ask if he really did. Remember that real banks won’t email you to ask for your authorised credentials or private information.
5. Figure out what your most valuable things are that criminals want.

Jim O’Gorman, a member of Social-Engineer.org, says, “When a lot of companies focus on protecting their assets, they do so from the point of view of their business.”
That is not always how hackers will try to break into your company. They always go after things that are important to them.
You should look at things from the attacker’s point of view to figure out what you need to protect. This means looking at more than just your product, service, or intellectual property.
“The best way to find out which of your assets thieves are most likely to go after is to use Independent Assessment.” — What O’Gorman says.
6. Look at the SSL Certificate

By encrypting data, emails, and communication, you make sure that hackers can’t get to the information in them, even if they intercept your communication. This can be done by getting SSL certificates from authorities that can be trusted.
Also, you should always check out a site that asks for personal information. Check the URLs to make sure the website is real. Sites with URLs that start with “https://” can be trusted and are encrypted. The websites that start with “http://” are not secure.
7. Testing for security holes

The best way to stop social engineering attacks is to do a pen test to find weaknesses in your organization and try to take advantage of them.
If your pen-tester is able to put your most important system at risk, you can figure out which system or employees you need to protect and what kinds of social engineering attacks you may be vulnerable to.
Find out how application penetration testing can help stop fraud.
8. Check for and install security updates

Cybercriminals usually look for flaws in your application, software, or systems to get to your data without your permission.
As a safety measure, you should always keep your security patches up to date and use the latest versions of your web browsers and systems.
This is because when companies find security holes, they fix them by putting out security patches.
Keeping your systems up to date with the latest release will not only reduce the chances of cyberattacks, but it will also make sure that your environment is cyber-resilient.
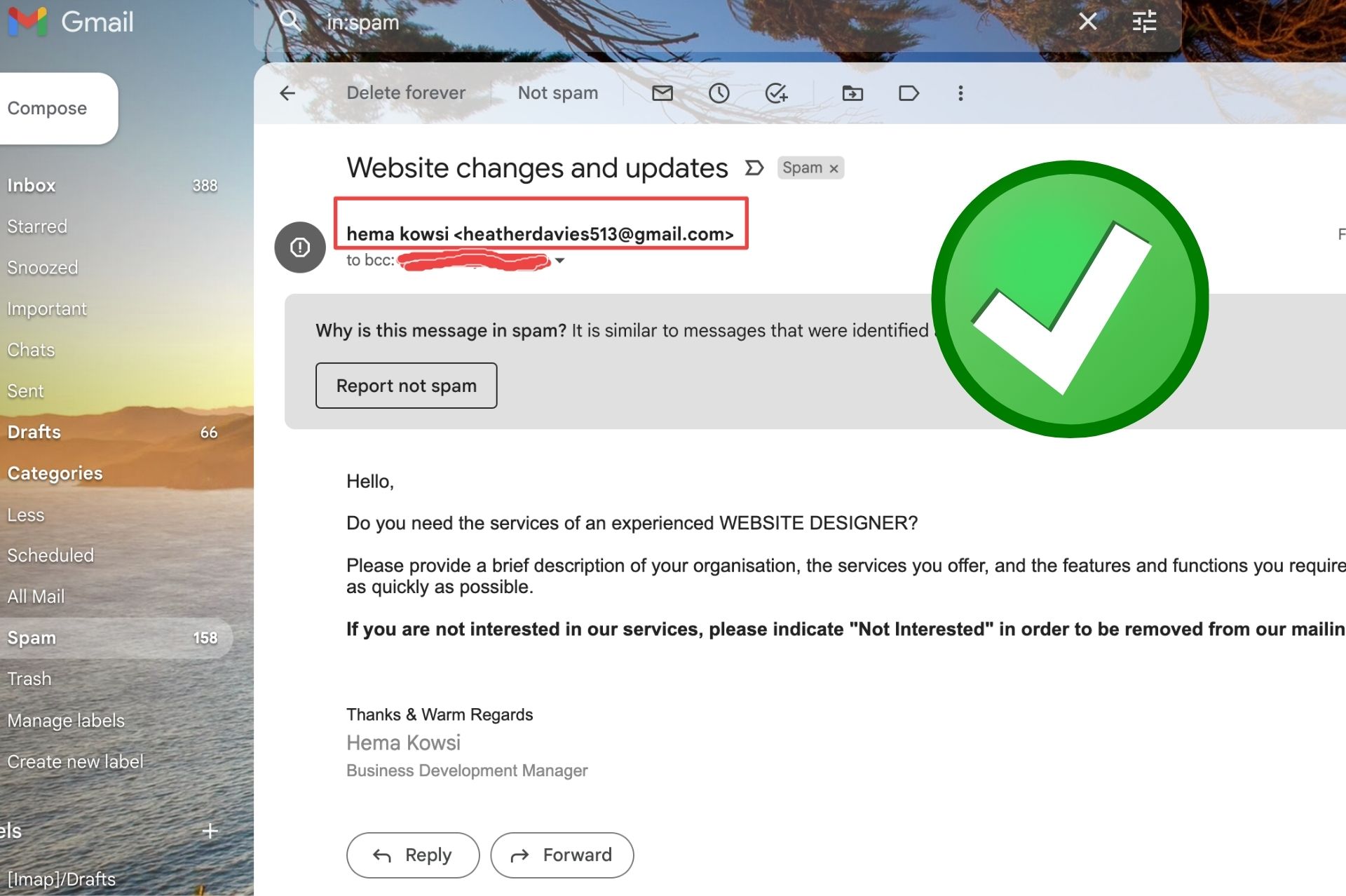
9. Enable Spam Filter
Turn on Spam filters and close the door on people who try to break security through social engineering. Spam filters are very important for keeping social engineering attacks out of your inboxes.
Most email service providers have spam filters that hold emails that look like they might be spam.
With spam features, it’s easy to put emails in the right category, and you don’t have to do the hard work of finding suspicious emails. This is the most effective way to detect and stop social engineering attacks.
10. Be aware of the digital trail you leave behind

If you share too much about yourself online through social media, criminals can get more information to use.
For example, if you keep your resume online, you might want to change your birth date, phone number, and home address. All of that information can help attackers plan a social engineering attack.
We suggest that you keep your social media settings to “friends only” and think twice before posting anything.
These are the effective way to detect and stop social engineering attacks.
Why Organizations Are Vulnerable to Social Engineering Attacks
Social engineering attacks are increasingly becoming a preferred method for hackers to access sensitive information and systems. Organizations are vulnerable to social engineering attacks because of the reliance on digital technology and human interaction. The human factor is the weakest link in any organization’s security. Social engineering attacks capitalize on this vulnerability by manipulating people to disclose sensitive information or perform actions that compromise security.
One of the main reasons organizations are vulnerable to social engineering attacks is the lack of security awareness and employee training. Employees may unknowingly expose sensitive information or be tricked into performing actions that can compromise security. In addition, employees may also be targeted by attackers who use social engineering techniques to gain access to the organization’s network or systems.
Another reason why organizations are vulnerable to social engineering attacks is the increasing sophistication of these attacks. Attackers are becoming more skilled at crafting convincing social engineering attacks that bypass traditional security measures such as firewalls and antivirus software. Using social media and other online platforms to gather information about employees and the organization also increases the effectiveness of social engineering attacks.
The Role of Employee Education in Preventing Social Engineering Attacks
Employee education is critical in preventing social engineering attacks. Education can help employees recognize and respond appropriately to social engineering attacks. Employees need to be trained on identifying social engineering attacks, such as phishing emails, fake websites, and phone calls, and how to report them to the appropriate authorities.
Employee education can also help in creating a security culture within the organization. This culture promotes security awareness and encourages employees to protect the organization’s information and assets. Employees who know security risks and are trained on best practices for securing information and systems can help reduce the risk of social engineering attacks.
The Risks of Not Taking Social Engineering Seriously
Organizations that do not take social engineering seriously are at significant risk of security breaches and data loss. Social engineering attacks can result in significant financial losses, damage to the organization’s reputation, and legal liabilities. In addition, these attacks can also result in the loss of confidential and sensitive information, which can have severe consequences for the organization and its clients.
Not taking social engineering seriously can also lead to regulatory and compliance issues. Organizations that fail to implement appropriate security measures can face fines, penalties, and legal action. In addition, organizations that fail to protect sensitive information can also face civil lawsuits from clients or customers who have been affected by security breaches.
Conclusion
Every day, social engineering attacks become more dangerous, and they are now one of the biggest cyber threats to businesses of all sizes.
You should take the right steps to protect your business from social engineering attacks. The most effective way to detect and stop social engineering attacks is spam mail and phishing attack.
Make sure your company has ways to quickly find security problems, keep track of what’s going on, and let your security team know so they can act right away.







